Update 4/26/17 :Due to requests for DOUBLEPULSAR scanning, we put together a page where you can check if you’re affected. Please patch, and adjust your firewall rules! Research from multiple independents have discovered a steady rise in infections around the globe with numbers around 344,000+ as of 4/26/2017 – BinaryEdge
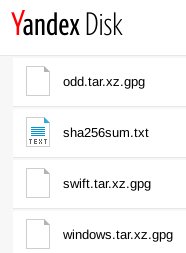
On April 14th a hacking group that originated in summer of 2016, called The Shadow Brokers, released their fifth leak and a collection of tools used by the NSA’s Equation Group. Leak titled “Lost in Translation” was made available via Russia’s cloud storage, Yandex Disk.
——————————————————————————————–
——————————————————————————————–
Leaked was a stockpile of Windows hacking tools. One of the tools being FUZZBUNCH. A tool utilized for executing exploit code against a remote target machine, similar to Rapid7’s Metasploit framework. Within FUZZBUNCH, there were multiple Windows exploits that were used to penetrate, and plant backdoors. Majority of exploits exploited weakness within Microsoft’s RDP (Remote Desktop Protocol) and SMB (Server Message Block) protocols. Among these tools, there is an implant called DOUBLEPULSAR. Countercept has a wonderful and in detail analysis, and for more info check out their blog post.
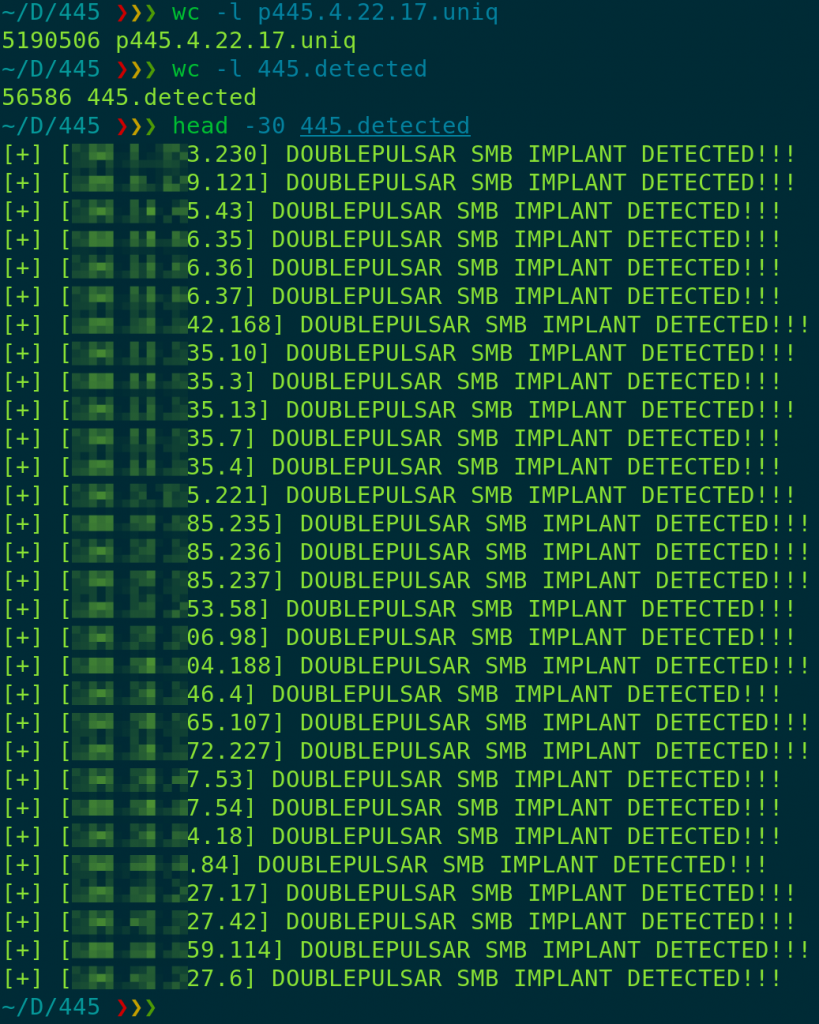
On April 18th 11:00 CTS, Below0Day conducted a internet wide scan utilizing masscan developed by @ErrataRob. Scan lasted for a little over 11 hours.
![]()
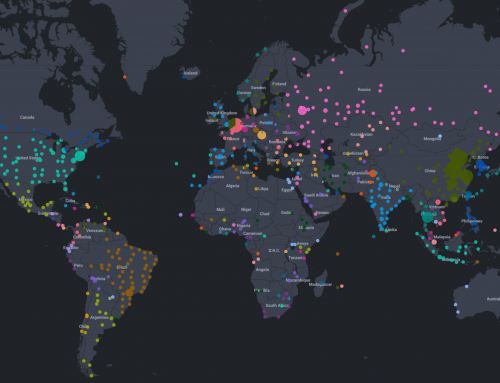
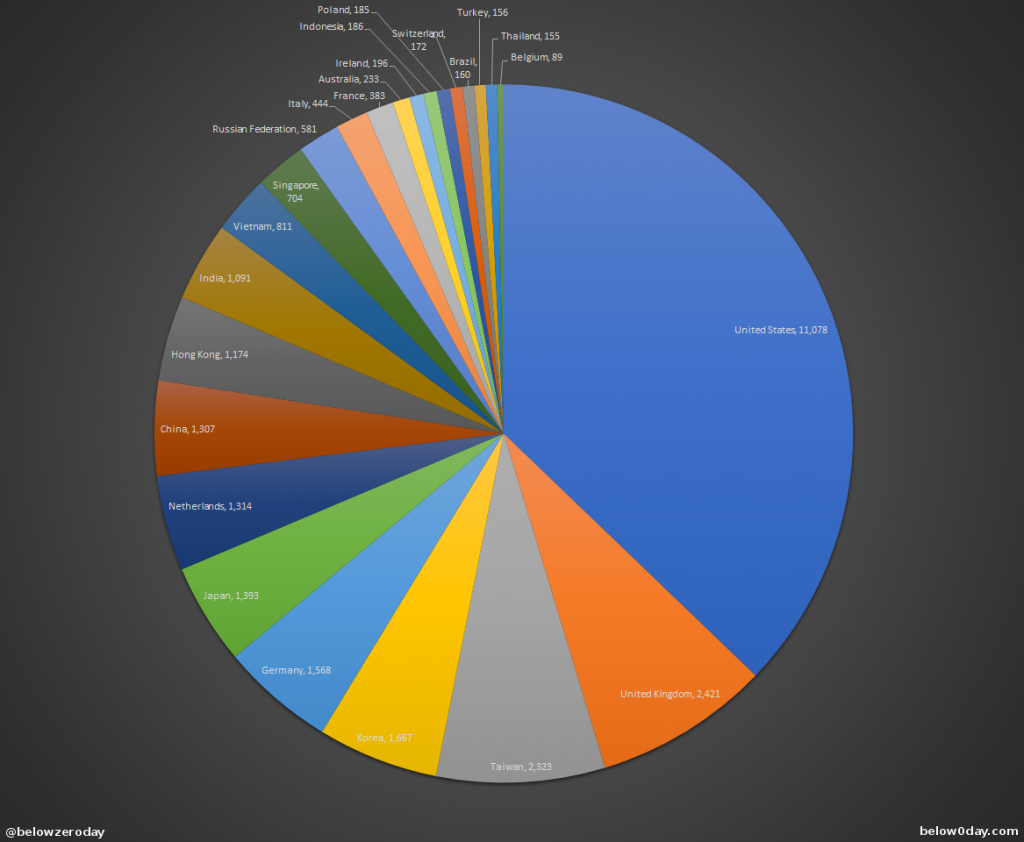
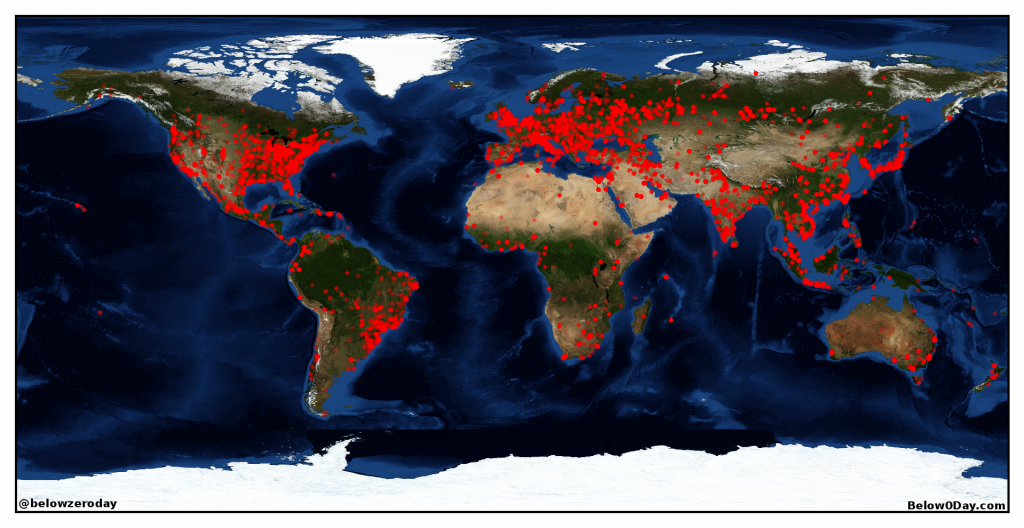
We took the final output from masscan, and cleaned it which resulted in a total of 5,502,460 unique hosts with an open port 445. We then turned to Countercept’s detection script, and fed it our masscan results. We were able to detect 30,626 hosts with DOUBLEPULSAR SMB implant. Once we got a final number of detected hosts, we used PyGeoIpMap to generate the world map of infections.
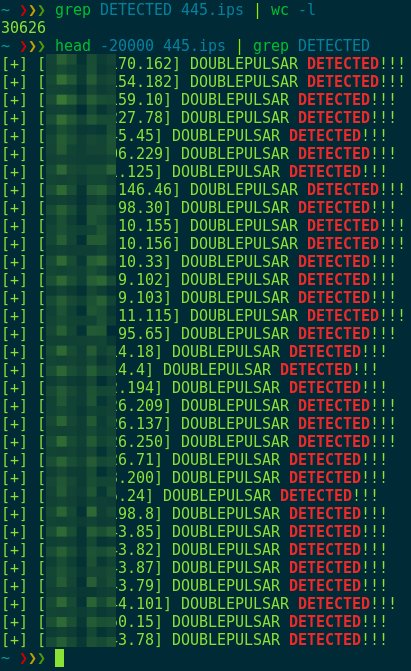
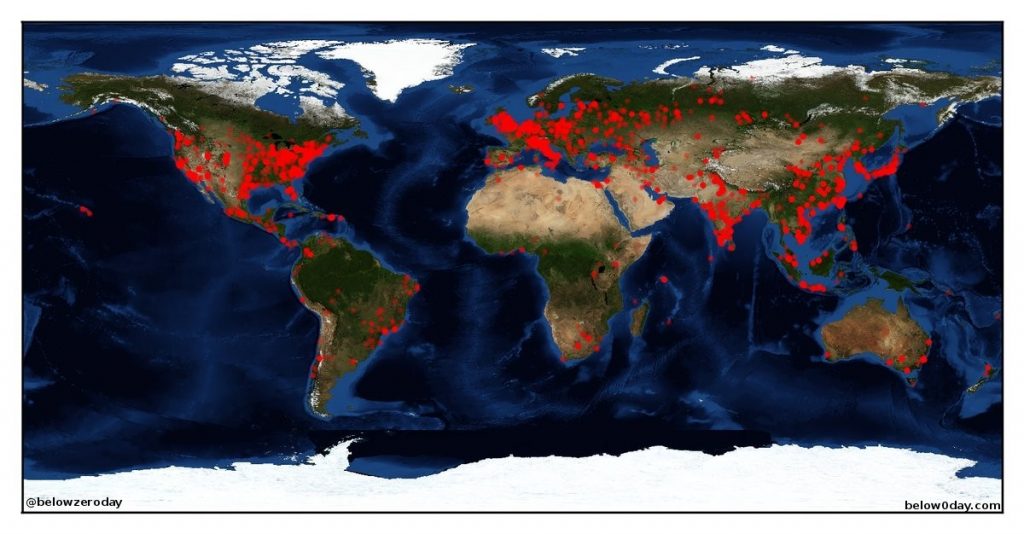
On the afternoon of April 21st, we initiated another masscan to get a new list of hosts with open 445 port. This time around we identified 5,190,506 hosts with port 445 open. We then ran Countercept’s detect script, and identified 56,586 hosts with DOUBLEPULSAR SMB implant.
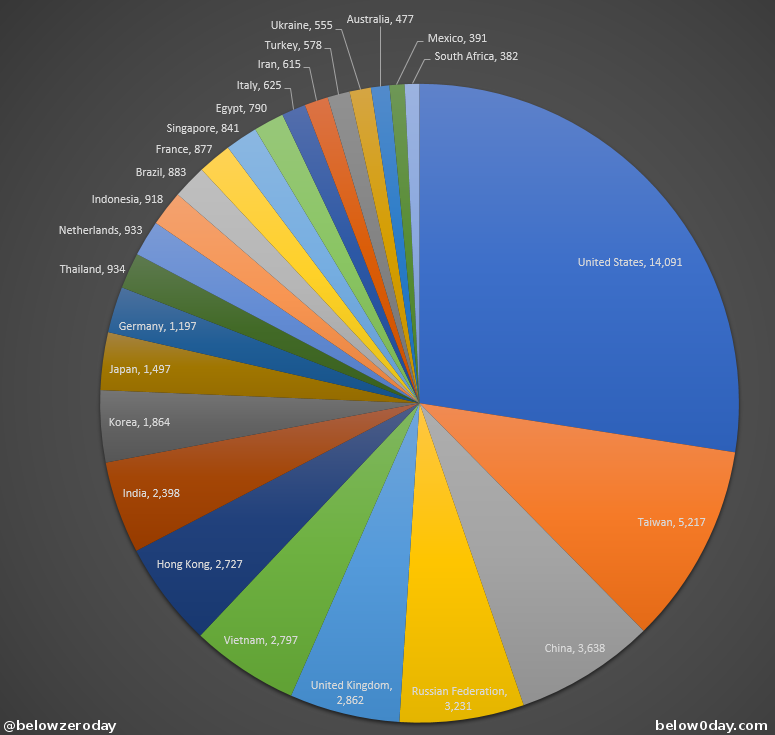
With such results, we can conclude that these numbers might only be increasing. For analysis and remediation, please contact us.